About this course
Overview
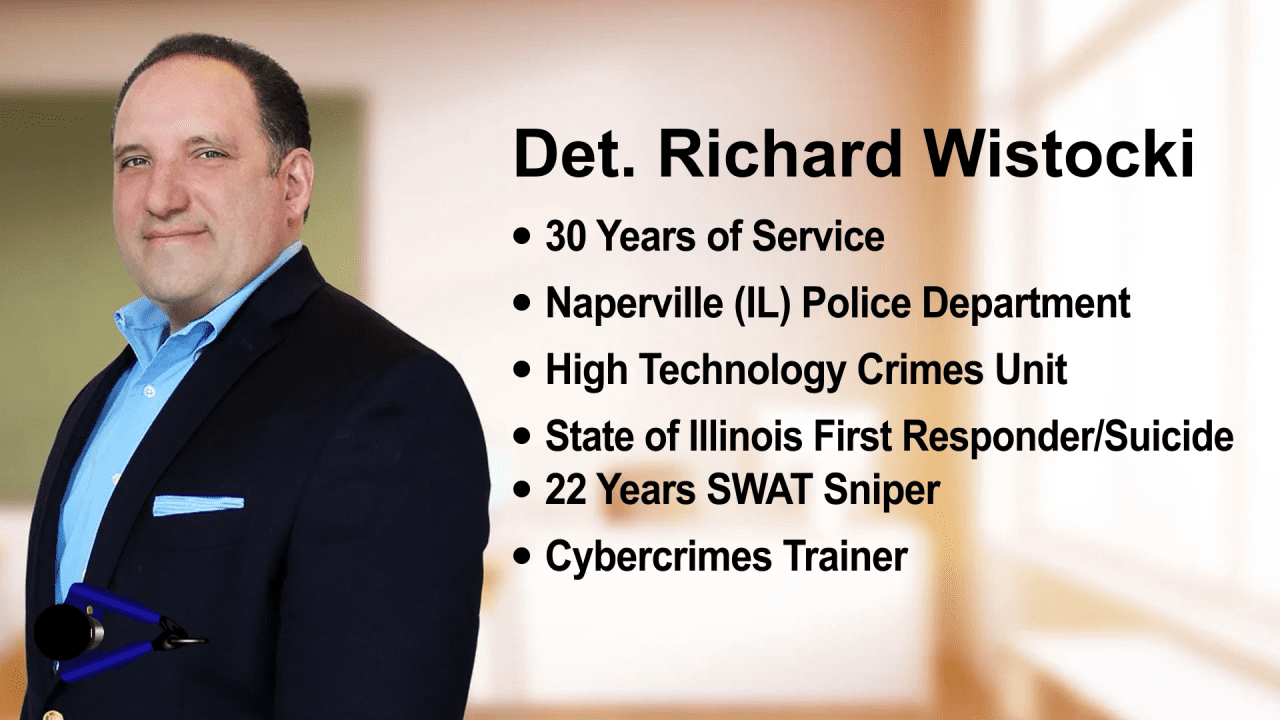
Det.(Ret.)Richard Wistocki, an expert in cybercrime, has developed a step-by-step plan of action that has identified potential active shooters via phone and computer forensics. As of this production, his teachings have thwarted an estimated
- 55 acts of violence
- 30 acts of swatting
- 13 school shooting threats
- 7 death threats
- 5 bomb threats
- 32 instances of ‘sextortion’ as of this production.
He calls it The Wistockian Theory.
The Wistockian Theory is a simple, easily learned course that has been of immense help to law enforcement officers via its approach. It involves taking the ICAC (Internet Crimes Against Children) standard of investigating internet crime and converting that process through the ECPA (Electronic Communications Privacy Act) and obtaining vital information to save the lives of students and faculty. Of course, it can be a critical approach to solving other internet-based crime, too. Initially it is triggered by so-called ‘leakage’.
LEAKAGE
Leakage is considered to be threats of violence or deadly plans communicated on any social media outlet or app; threats (text or video) that are ongoing and appear to the recipient/reader as being real. They are ‘red flags’ but, often, are overlooked by those closest to the subject. The Parkland shooting/student murders is a critical example Rich often cites, in which the mass shooter posted multiple videos and texts well before his horrific shooting spree (leakage). Despite it, one of the worst mass murders of students occurred.
Course Video Preview:
